Home > Projects > Cybersecurity Awareness
Cybersecurity Awareness
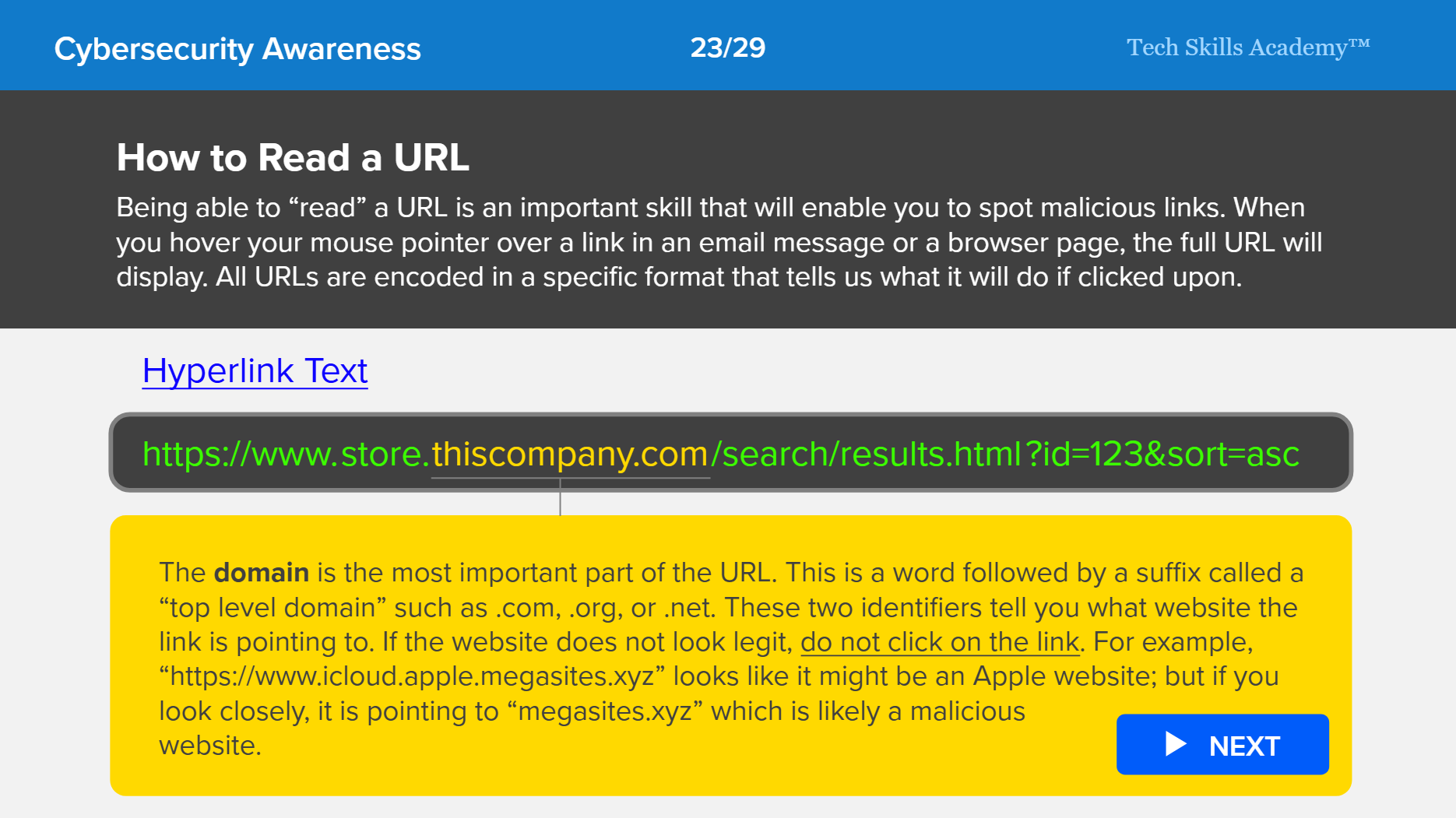
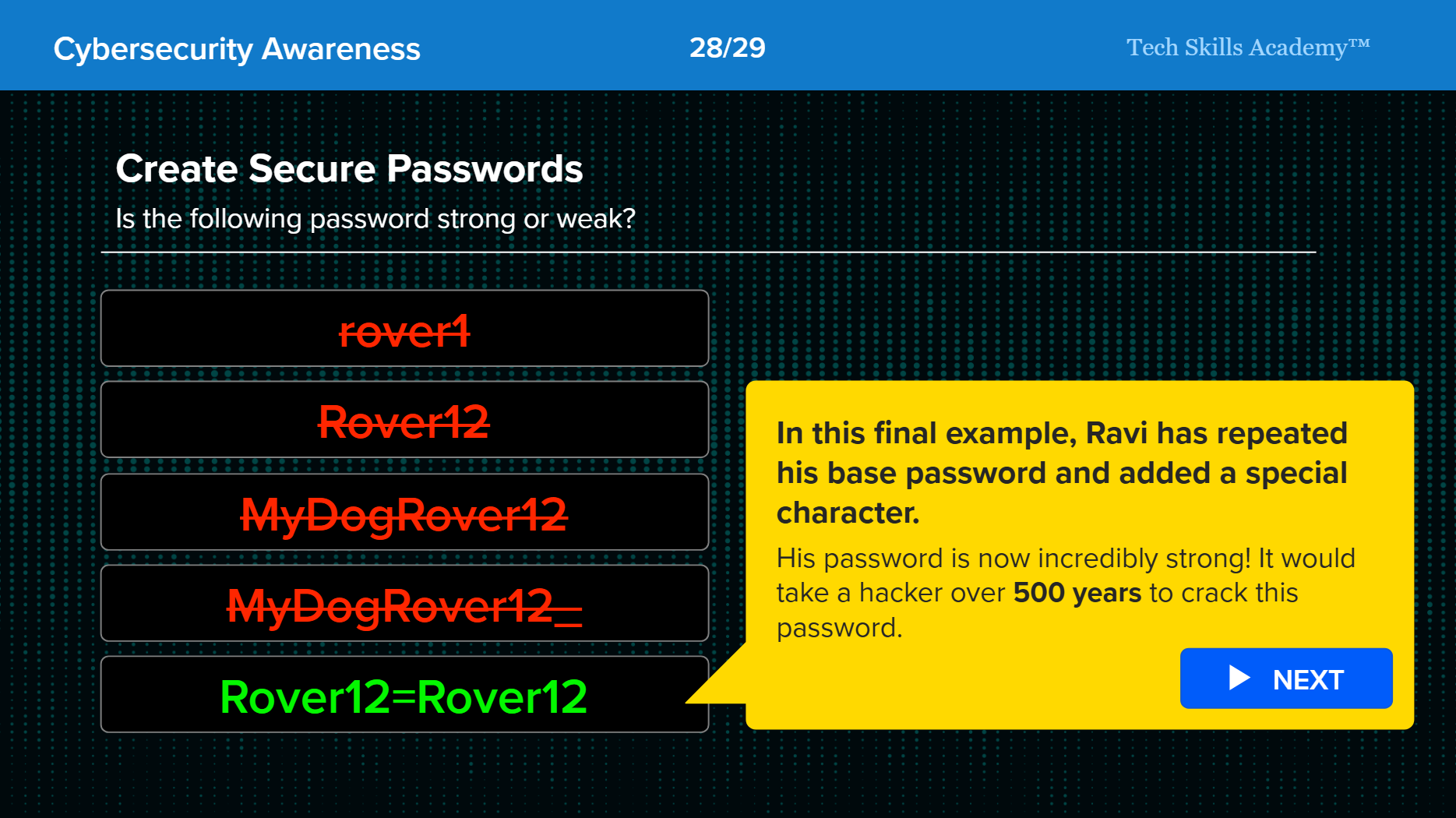
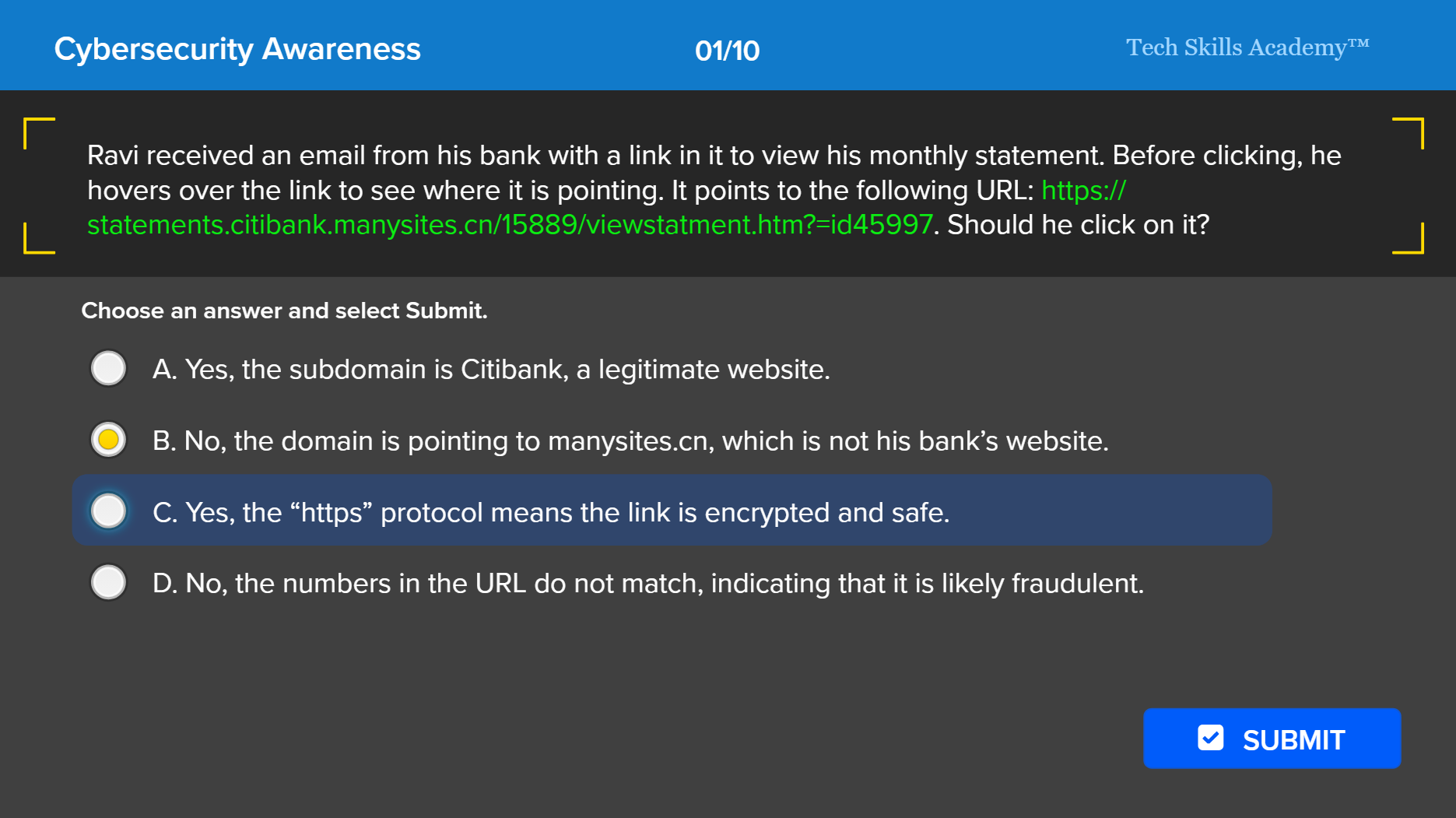
The Cybersecurity Awareness course provides a comprehensive foundation in digital safety by teaching participants how to think like a hacker to better anticipate and mitigate potential risks. The course covers critical areas of defense, including maintaining security at work and home, protecting sensitive information, and recognizing social engineering tactics. Practical skills are emphasized throughout the module, such as identifying phishing emails, reading URLs correctly, managing secure passwords, and navigating social media and public networks safely. The course uses sound instructional design principles to ensure an effective learning experience, including a knowledge assessment to validate proficiency in the topics covered. Select View Course to launch the module.
Development Tools:
Articulate Storyline 360
Adobe Photoshop, Illustrator
Adobe Firefly
Notebook LM
Revoicer AI Text-to-Speech Generator
Project Summary
This is a re-creation of a course I developed for one of the largest financial corporations in the world. As a global company with a high-profile brand, and tens of thousands of employees they are under constant attack from cyber threats within and without. As a senior instructional designer, I was tasked with the annual Cybersecurity Awareness online course development. This is a required firmwide course for all employees and contractors, and a critical piece of the firm’s cybersecurity strategy.
Instructional Design Approach
Analyze Phase
I used the ADDIE instructional design model for this project. The Analyze phase started with a survey of the previous years course and level 1 reporting data. Then I began working with a small team of cybersecurity SMEs. In these meetings, we discussed the latest research and techniques that hackers and cybercriminals use to steal data and breach systems. This is a rapidly evolving area of risk. We wanted the course to address the most up-to-date tactics and attack techniques of hackers. We also wanted to present the course in a new and innovative way.
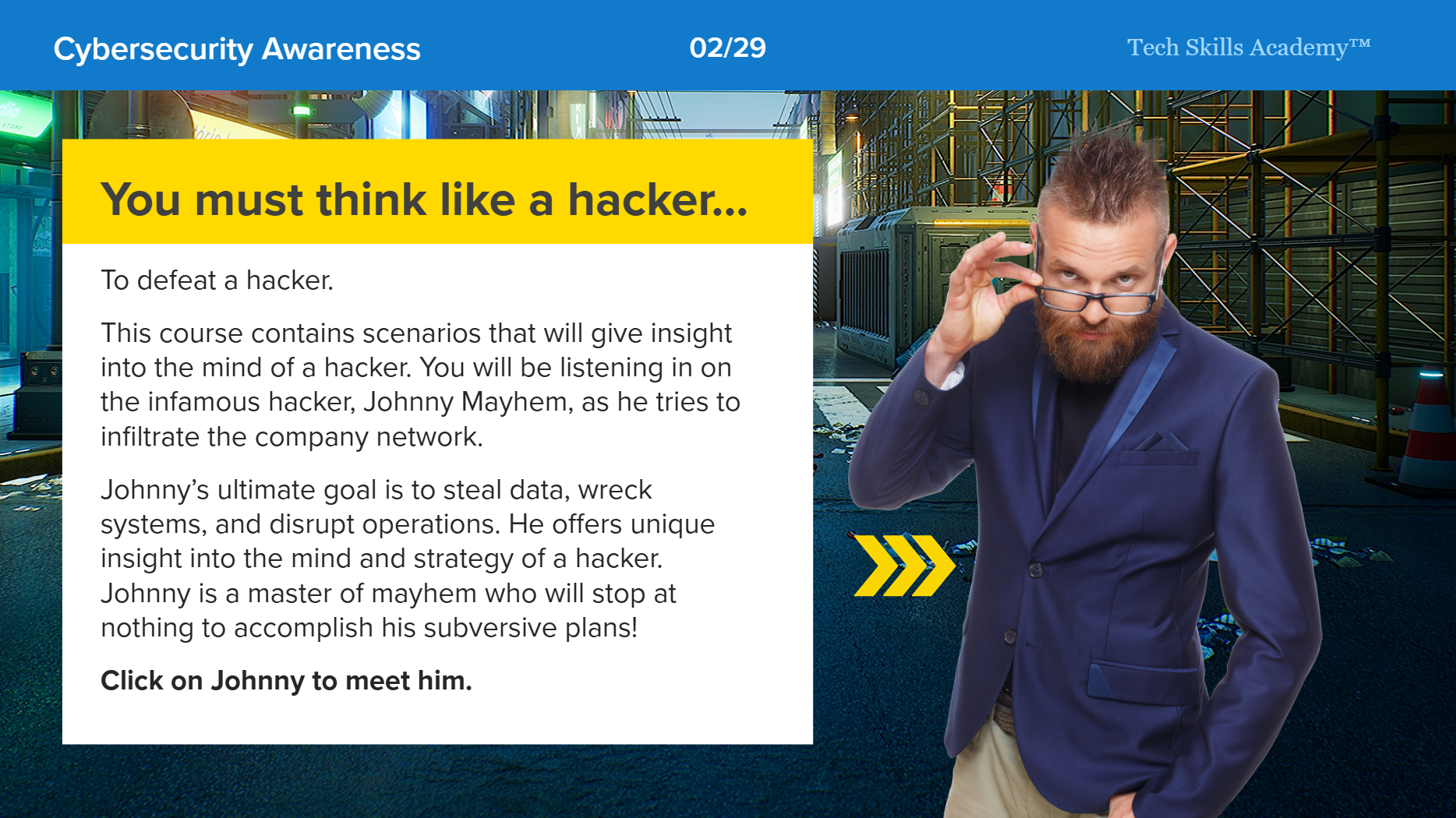
I had a creative idea for a different approach that would make the learning more interesting and drive learner engagement and knowledge retention. The idea was to present the information from the hackers point of view. I created a hacker persona, dubbed “Johnny Mayhem,” that would be the antagonist. The learner would follow Johnny as he attempts to infiltrate and hack people at the bank. This provided opportunity for interesting and imaginative dialogue and storytelling elements. A prototype was created and approved by stakeholders and senior management.
Design Phase
The Design phase started with a storyboard outline of the course. I worked with the SME’s to create a logical flow in the course that covered three critical areas of cybersecurity awareness: the work environment, at home, and in public. The SME team articulated the risks and scenarios involved. I began to think of creative ways to present the information. I wanted to draw in the learner with interesting and interactive diagrams and puzzles that would make them feel like they were “doing” and not just learning. We also had to work with stakeholders in regulatory and compliance. We needed to make sure that course was adequately protecting the bank and it’s employees.
Upon completion of the Design phase, we had an approved storyboard as a map to begin development of the online course.
Develop Phase
The Develop phase describes the actual building of the online course in Articulate Storyline 360. The course needed to be visually engaging and high-fidelity. The goal was to engage the learner’s attention via sight, sound, movement and emotion.
Sight - Carefully selected stock and generative AI imagery with a realistic visual style
Sound - Alternating male and female AI generated voiceover supported by sound effects
Movement - Animation cues every 4 to 5 seconds, keeping the learner’s attention
Emotion - Telling a story that makes people feel something
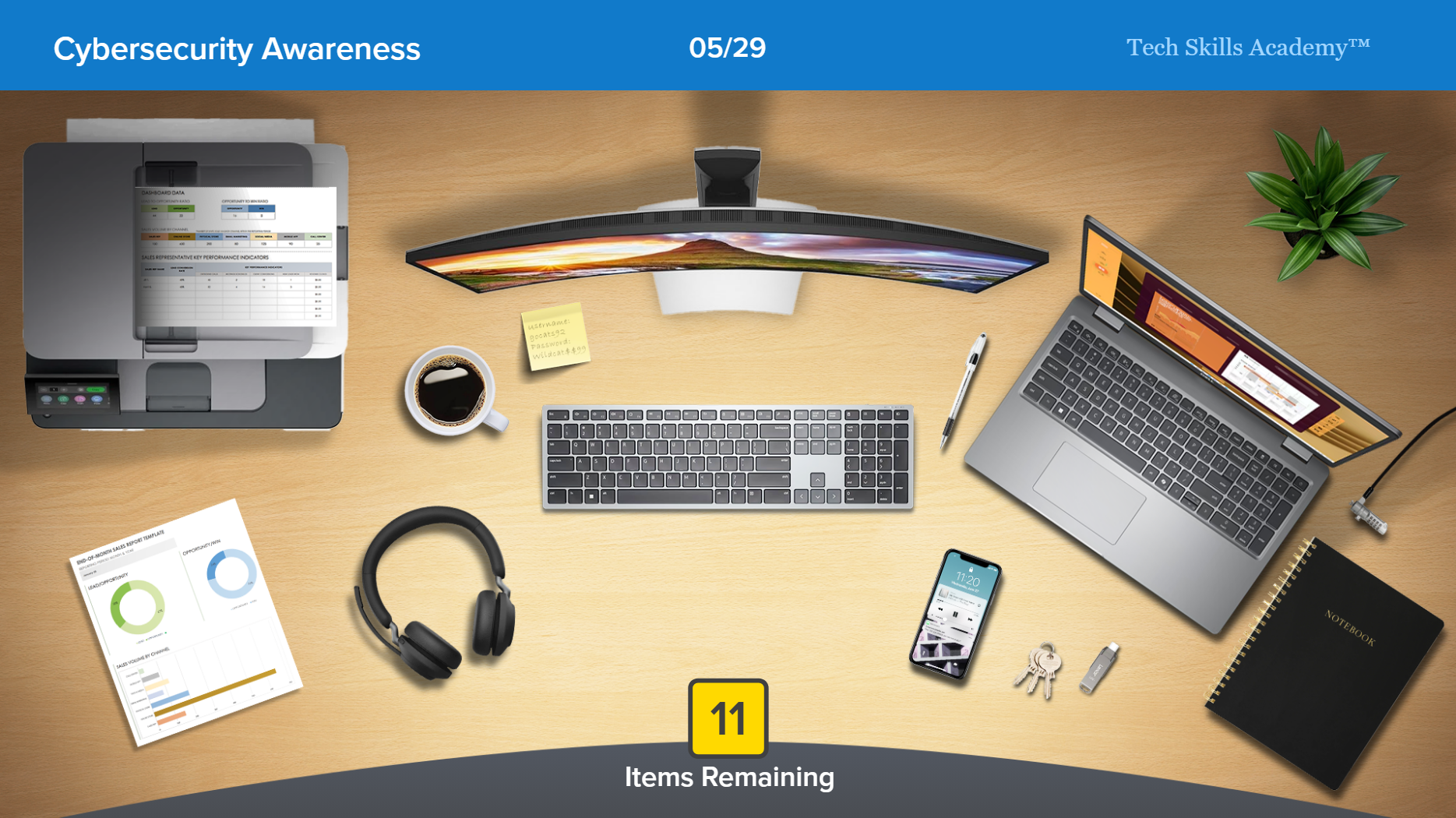
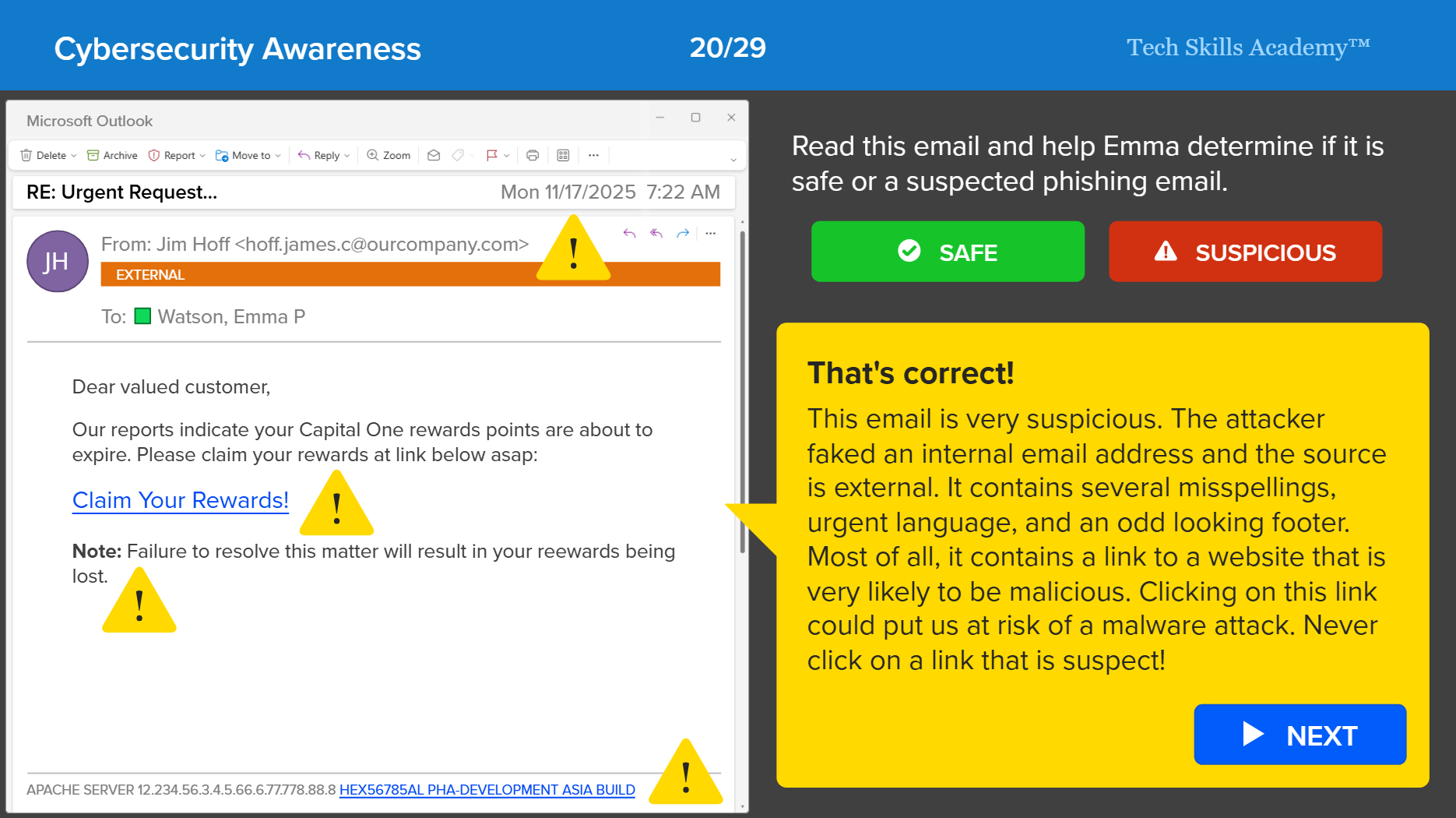
The course leaned heavily on “click-to-reveal” type interactions that gives learners the reward of finding information. Elements of gamification are also introduced with integrated knowledge checks and progress counters.
The original course also featured a “test-out” that allowed learners the opportunity to demonstrate knowledge of the course content and reduce training time. The course was developed in three distinct phases:
Alpha - The first iteration of the course built according to the storyboard specifications.
Beta - The second iteration of the course, incorporating stakeholder guidance and feedback from the Alpha version.
Gold - The final iteration of the course, including all integrated feedback from prior phases.
At the completion of this phase, the course was signed off on, and ready for implementation.
Implement
The Implementation phase included the following:
QA and testing of the course in the LMS stage environment
Deployment to production
Course creation in the company learning portal
Staggered course releases scheduled to mitigate server load during rollout
A response plan to identify and fix any reported issues reported by learners
Evaluate
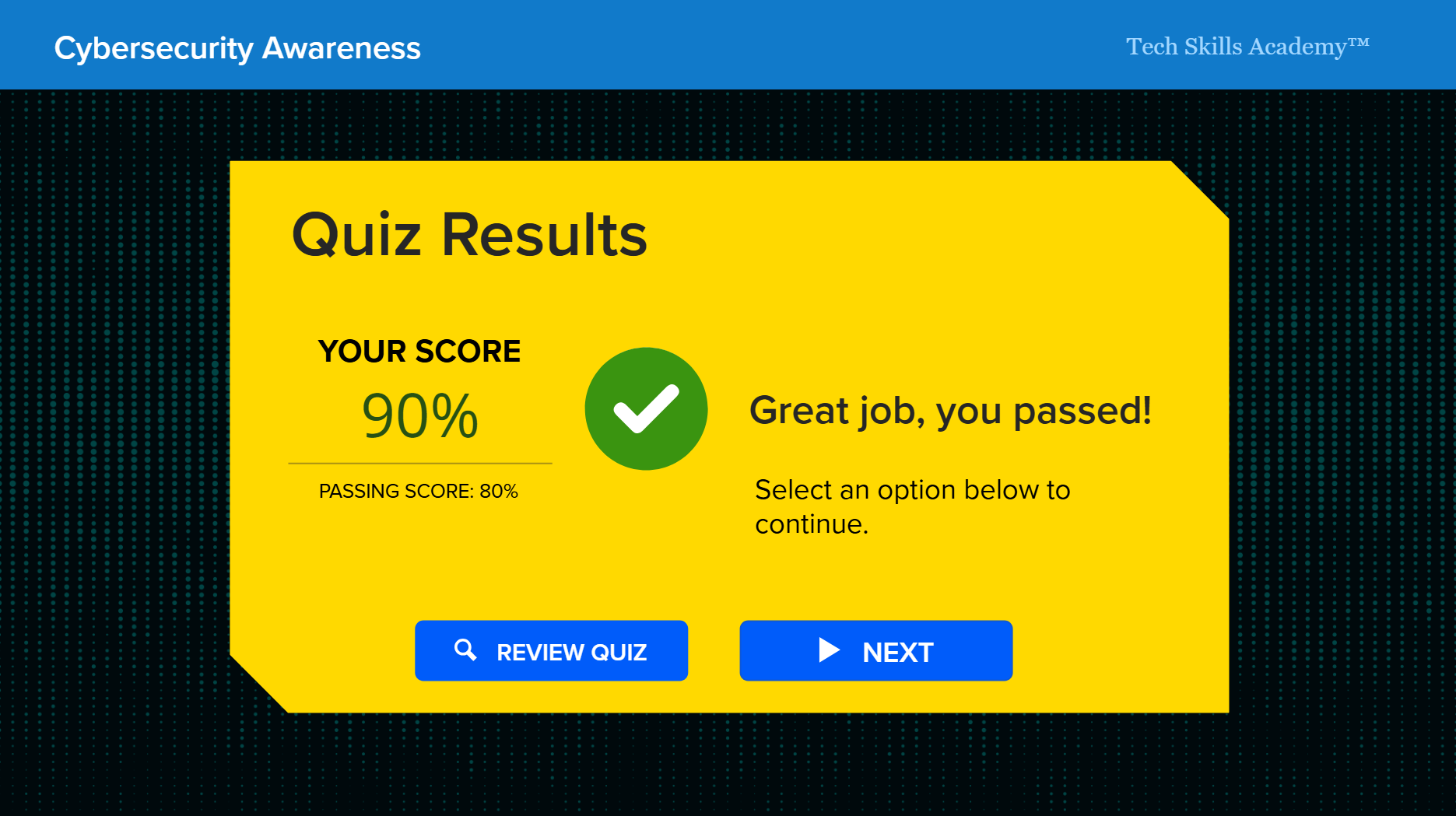
In the Evaluate phase, the course owner was tasked with oversight of the level 1 reporting data gathered from the course. This included rating on a five point scale and open learner feedback. They also monitored KPIs to measure the impact of the course on cybersecurity incidents. Learner feedback resulted in some minor updates to the course build. Overall percentage of learner satisfaction was in the mid 90s.
Conclusion
This course was very successful from a measurable business standpoint. The course was part of a broader strategy to reduce data loss and cybersecurity incidents at the bank. Cybersecurity reported substantial reductions in successful phishing attacks and DLP incidents. This course is a great example of how sound Instructional Design principles paired with a creative, fun approach to course design can produce real, measurable business results.
Johnny Mayhem Introduction
Securing your desktop at work
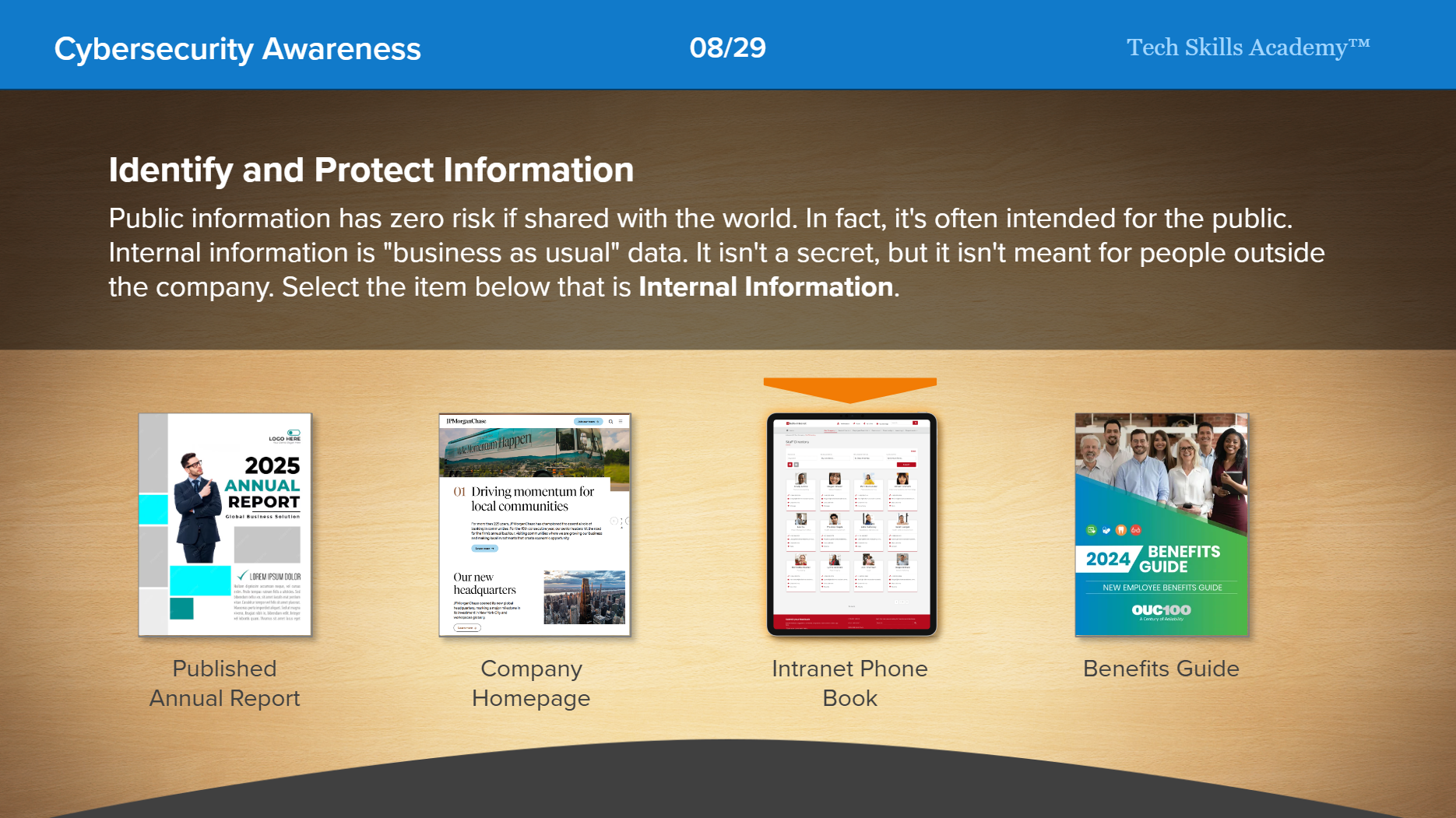
Securing and classifying information
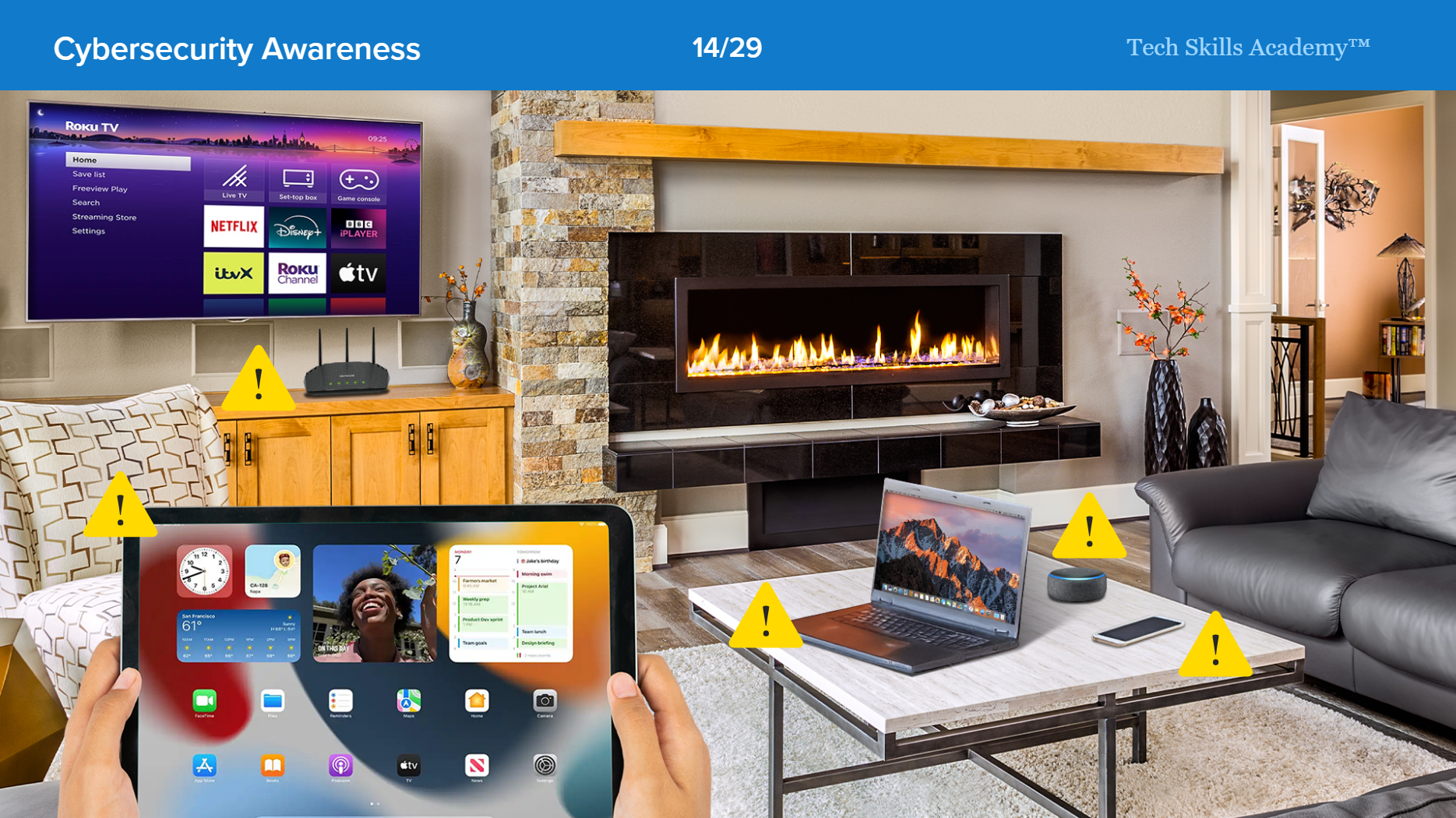
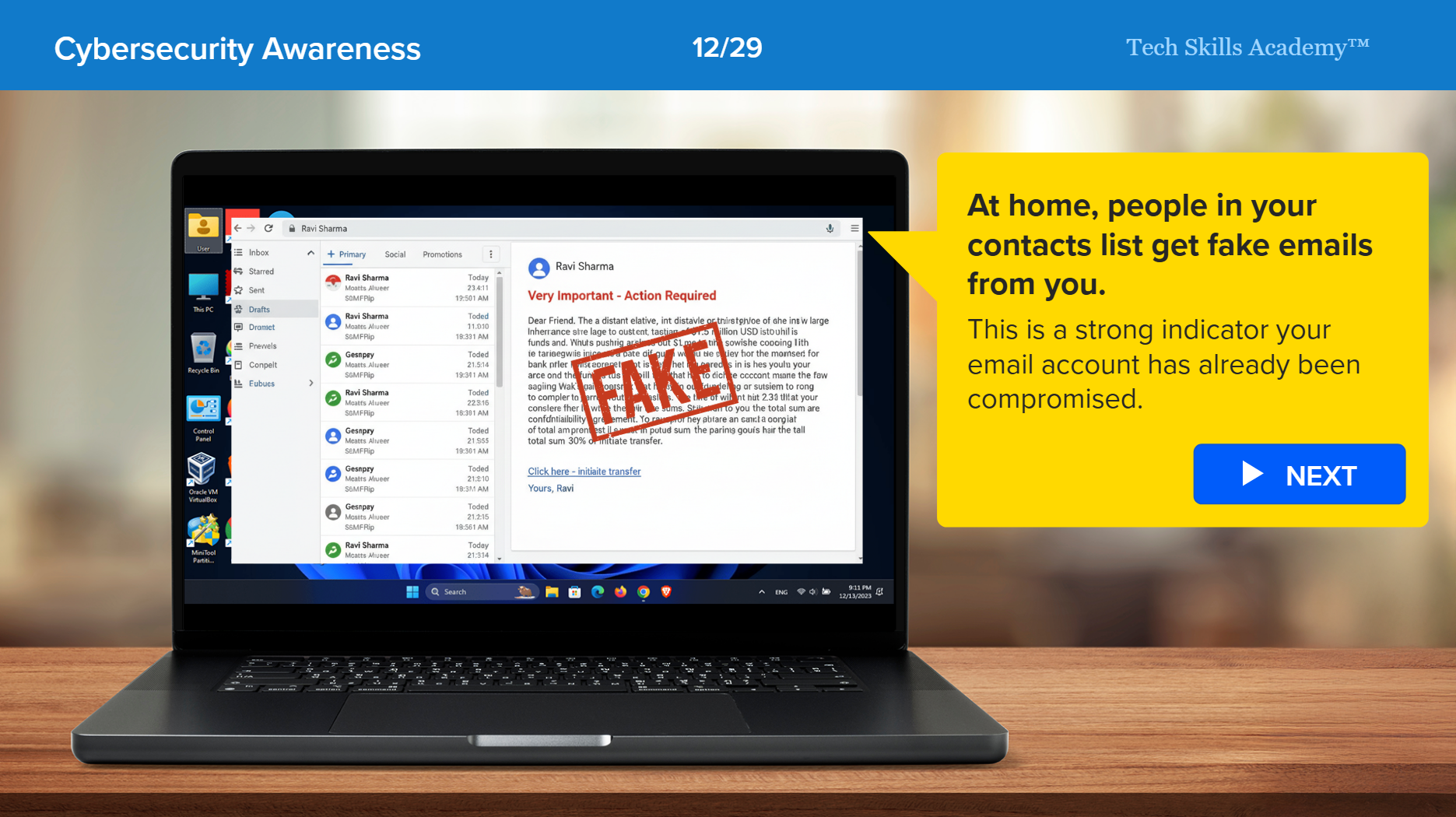
Securing your devices at home
Spotting cyber attacks
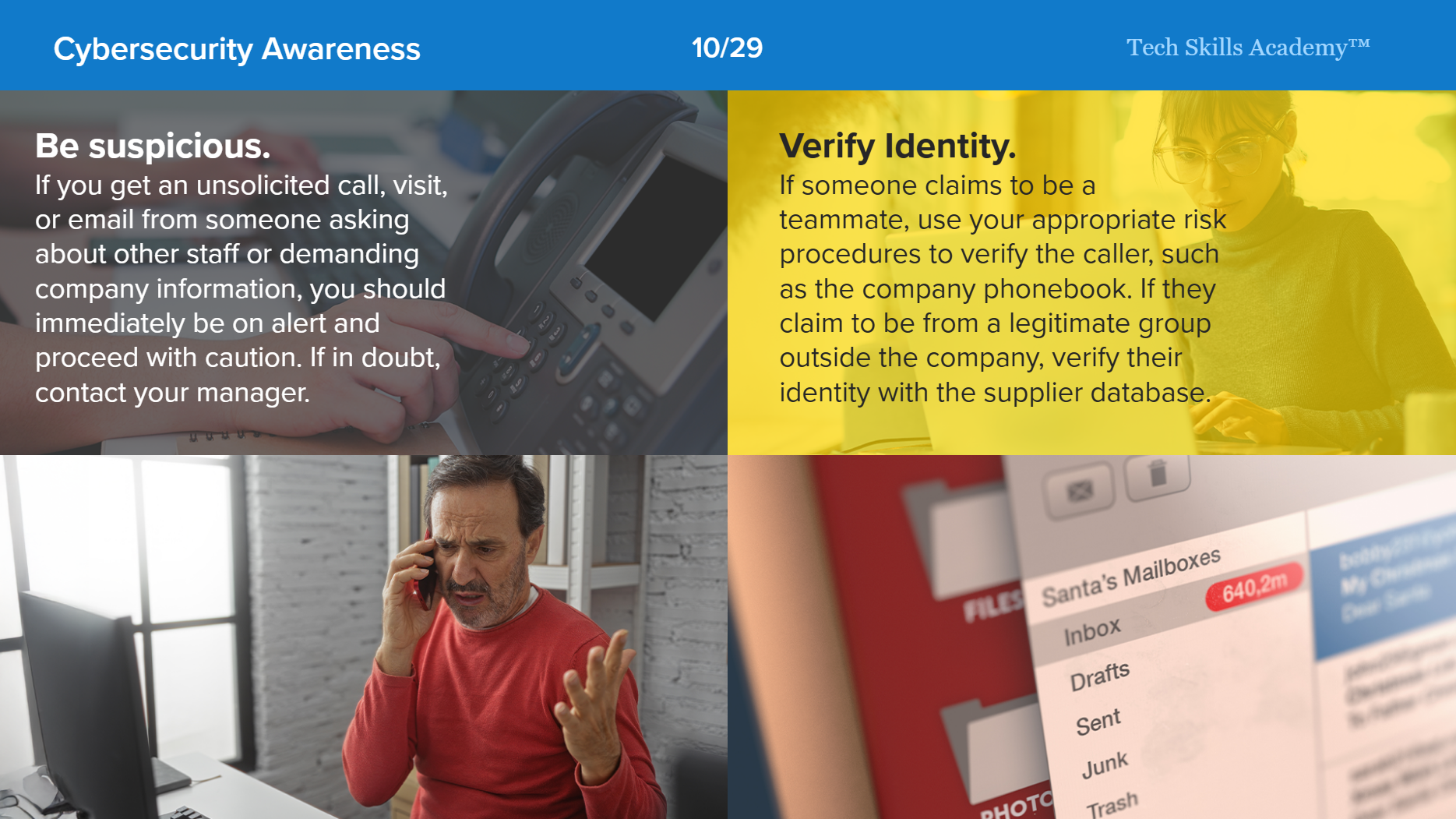
Spotting social engineering
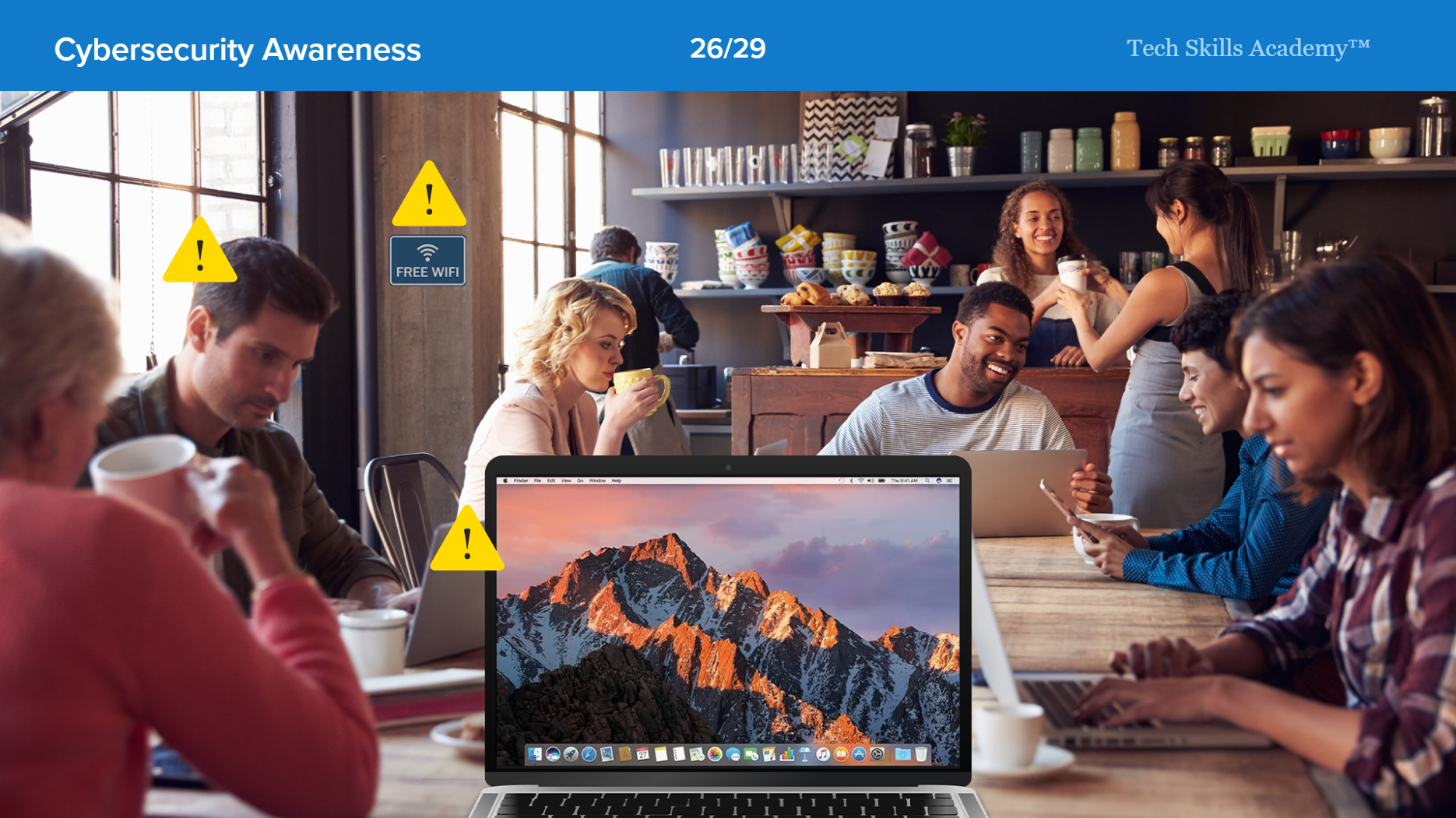
Staying secure in public spaces
Securing your social media sites
Recognize phishing emails
How to read a URL
Creating secure passwords
Assessment
Assessment results